This technique will be taking advantage of Port 139. Most of the time,Port 139 will be opened in the computer. First of all, we will do a port scanning at the target computer....
As shown in the fig. port 139 is opened.
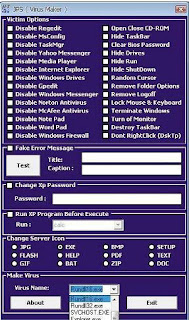
Now you will need both of these following tools:
USER2SID & SID2USER and NetBios Auditing Tool
User2sid and Sid2user are two small utilities for Windows NT, created by Evgenii Rudny, that allow the administrator to query the SAM to find out a SID value for a given account name and vice versa. User2sid.exe can retrieve a SID from the SAM (Security Accounts Manager) from the local or a remote machine and Sid2user.exe can then be used to retrieve the names of all the user accounts and more. These utilities do not exploit a bug but call the functions; Lookup Account Name and Lookup Account Sid respectively. These tools can be called against a remote machine without providing logon credentials except those needed for a null session connection. These tools rely on the ability to create a null session in order to work.You can get both of them on the Internet.
After you get both of them,put them in the C:\ directory.
For connecting You now need to create a null session to the target computer.
Now open the Command Prompt and browse to the USER2SID & SID2USER folder.There will be 2 tools inside it,one will be USER2SID and another one will be SID2USER. We will first using USER2SID to get the ID.
We will test against the Guest account because Guest account is a built in account. After we get the ID,we need to do some modification on the ID. We take the ID we get from the guest account and modified it become
“5 21 861567501 1383384898 839522115 500″.
Please leave out the S-1-,leave out all the – too.
Now you will see that you get the username of the Administrator account. In this case,the Administrator account is Administrator. Create a text file called user.txt and the content will be the username of the Admin account.
Prepare yourself a good wordlist and create text file pass.txt.
Now put both of them in the same directory with the NetBios Auditing Tool.
Now we are going to crack the Admin account for the password in order to access to the target computer. Browse to the NetBios Auditing Tool directory.
Press on enter and the tool will run through the passlist.
In this case,I have get the password. In order to proof that I can get access to the target computer using this password.
After you press enter,it will prompt you for the username and password.
Target C drive will be on your screen.
thats it........